What is Security
The safety of information and their systems against illicit access, disclosure, use, amendments, or destruction in order to provide privacy, veracity, and availability is called information security.

-
Confidentiality
According to information security, confidentiality is described as “when any information is not shared, disclosed or sold to unauthorized or anti-social person”
-
Integrity
Information security says data integrity is all about retaining and promising the accuracy and entirety of data over its complete life-cycle.
-
Availability
Any information must be available when it is purposefully needed to be served.
-
Risk Management
Risk management is the procedure of recognizing threats and vulnerabilities which could affect the information resources utilized by a company in accomplishing business objectives, and deciding what countermeasures can be taken in minimizing risks to a satisfactory level, based on the importance of the information resource to the company.
Why Information Security
Information security, aka InfoSec, is the practice of protecting information from illegal access, perusal, inspection disruption, modification, recording or their destruction. It is a common term used despite the form the data (e.g. electronic, physical).
BASIC INFORMATION
Computer system threats can be identified in numerous forms. Some of the most generalized threats are software breakage, theft of integral property, theft of identity, theft of information, damage, phishing attacks, and Trojan horses, viruses, worms and extortion of information.

Our Services
We are a Leading Information Security Services, Training and Consultancy Company

- Network
- Websites
- Social Media
- Emails

- Data Loss Prevention
- DDOS Protection
- Data Encryption
- Cloud Infrastructure

- Security Awareness
- Employee Training
- IT Consultancy
- Security Consultancy

- Network
- Employee Activities
- Social Media
- Search Media
Security
The protection of information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction in order to provide confidentiality, integrity, and availability.

-
Network
Network security comprises of the practices and policies which are employed to protect and monitor unrecognized access, mistreat or denial of a computer network and its accessible resources.
-
Website
We ensure the safety of your websites which are unfortunately risked to security threats and other networks to which web servers are connected.
-
Social Media
We protect Social Media Profiles from hacking, spamming, exploitation, attacks or misuses
-
Emails
Email security is a most viable business priority, with the increasing threat of viruses spam, hackers, phishing and identity theft it is eminently needed to protect business emails.
Monitoring
We monitor the Digital Look for modifications and vulnerabilities affecting your business.

Network monitoring constantly checks a computer network for those attacks, slow or degrading components and that informs the network administrator to manage and repair the same.

Employee monitoring helps in checking employee activities such as their performance, and also protecting trade secrets, and identify other security problems.
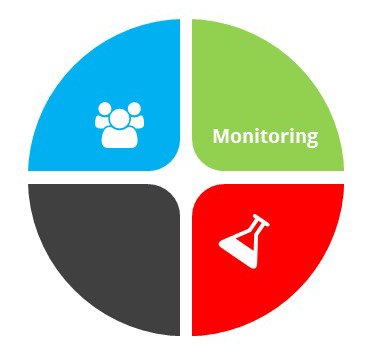

Social media platform is made for private, either for personal or business use. As a web accessed channel, these are also prone to attacks, spam, intrusions and other activities. We protect your social media profiles.

Search engines are the lifeline of the internet. Our security services help those search media in protecting them. We keep checking and protecting search mediums.
Protection
We also protect from unexpected threats, data loss and nofficial access to your personal information system.

Our Data loss prevention is a strategy for ensuring that end users would not send sensitive or significant information outside the corporate network.

We provide protection services against DDoS which is a kind of DOS attack where numerous compromised systems often infected with a Trojan, are utilized to aim a single system creating a Denial of Service (DoS) attack.

Our Data Encryption ensures that only particular person/s is authorized to receive or send data using the decryption key.

Cloud Infrastructure is cloud computing form that serves virtualized computing resources over the Internet. With our Cloud Infrastructure, we provide great scalability, security, access, centralization, control and improved management of information for your company’s data and services.
Consulting
We have Government and Corporate Experience and meet the utmost level of standards of Skill, competence, and discretion.

We create Security awareness, the knowledge, and attitude which help our clients in protecting their security concerns of their information systems.

We create Security awareness, the knowledge, and attitude which help our clients in protecting their security concerns of their information systems.

We create Security awareness, the knowledge, and attitude which help our clients in protecting their security concerns of their information systems.

We create Security awareness, the knowledge, and attitude which help our clients in protecting their security concerns of their information systems.
Our Clients